OTP Verification
Two-factor authentication (2FA) has become a standard across varying verification requirements. If you try to log into Amazon using the same device, the user can perform re-authentication by sending an SMS to verify the user's identity. It is the same for emails, social networks, online wallets and streaming platforms. It's important to ensure that a user can easily and safely identify and report suspicious behavior and protect them from misuse.
Some applications validate and allow their customers through an identifier, called an OneTime Passcode or an SMS. This article teaches about Twilio verification for SMS users. You build a pared-down frontend using JavaScript and HTML, and you build a Node.js backend hosted in Twilio Functions and scaffolded using Twilio Serverless Toolkit and other components.
More importantly, security isn't among the advantages of SMS OTP anymore either. The SS7 technical flaws in the mobile network are frequently used for interception and rerouting of SMS messages that contain OTPs. These issues are just part of the reason that SMS OTP for verification and authentication has been called a deprecated authentication solution for some time now.
This is true of email, social media accounts, e-wallets, streaming platforms etc. as well. This form of User Verification is an important way of preventing fraud and protecting customers from misuse/abuse of their information. During present times, when hacking of online applications and theft of confidential information like passwords and PINs are happening every day, 2FA adds another layer of security.
Set Twilio functions
Run the command following from the project file to create a function service. This can be done by creating an account on your machine called verio-demo. There are some boilerplate folders and file formats for Twilio Function. You can store front-end code files inside a folder verification/asset, and you can also store front-end code files inside a folder verify demo. A few more things will be noticeable. Env files in the demo folder. These files have been prepopulated with Twilio's SID and Authorization Number.
Test out your app
We're ready to use your new app! Navigate to the Verify demo directory on the console. This will start a local server on Port 3000. Please visit the site in your browser for a preview of your app. Put your phone numbers into the field, starting with the country code and clicking the Submit button. When you click on the Send button, phone numbers forms can be replaced for validation. Afterwards, you will receive OTP by SMS. Please submit your OTP for verification at the following website:
Deploying your Twilio functions
Your App is currently based solely on your laptop. If you want to deploy locally hosted applications built on Twilio Functions, then you can run the following commands to deploy the application to public servers.
How it works Phone verification

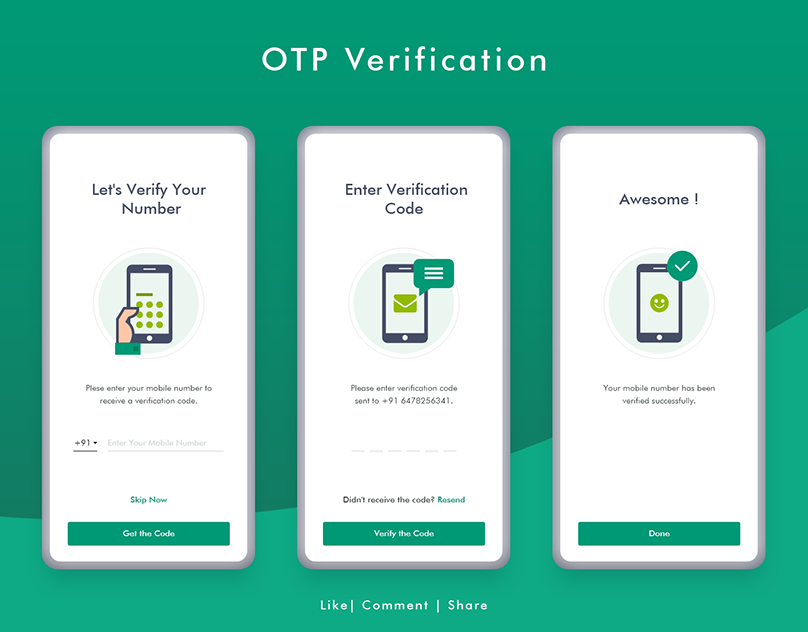
User enters their phone number or email App generates an authentication token App sends the token via selected channel to the user User enters the correct token App verifies the token For more information, check out this blog post on serverless phone verification . For interface best practices including retry logic and channel fallback, check out best practices for managing retry logic with SMS 2FA .
OTP security tokens can be implemented using hardware, software or on demand. Unlike traditional passwords that remain static or expire every 30 to 60 days, the one-time password is used for one transaction or login session. How to get a one-time password When an unauthenticated user attempts to access a system or perform a transaction on a device, an authentication manager on the network server generates a number or shared secret, using one-time password algorithms.
This can be done by configuring bulk SMS API. Setting up OTP verification can give users more promising and safe environment to use mobile phones for business, banking, shopping and many other important transactions. Authenticating the users, password resetting, upgrading the authorization and so on are the instances where enterprise users demand OTP verification.
Customer identity verification
Customer Identity Verification is the process of verifying an individual's identity by comparing it against a reliable source. This is often done to protect businesses and customers from fraud and other security risks. It can include checking government-issued identification such as a driver’s license or passport, using biomet.
For customers, SMS is one of the simplest ways of authentication. Almost everyone has a mobile phone that can receive text messages. SMSes are easy to use and free to receive. The technology has been around for over 25 years, and most mobile phone users are comfortable using it. For enterprises, too, it offers several benefits.
Service provider
As a user, my onboarding experience is ruined. I haven't even started using the app or service yet, and it's already not working as expected. As a service provider, I risk losing the user, I lose resources on the SMS OTP service, and “every once in a while” is way too often for the code to never arrive. Whatever type of service this is, it's crucial that I verify my users' mobile phone numbers.
Mobile text messaging is one of the ways of receiving an OTAC through a mobile phone. In this way, a service provider sends a text message that includes an OTAC enciphered by a digital certificate to a user for authentication.
Creating a new Verify service
Click on the verification section within Twilio Console. Click on blue+ (+) to add a service. A modal menu will show where the user has to give the name of the service they offer. Call that Nodedemo, or another short descriptive name that you choose.. You will see the settings for the service after you create the service. In the lower portion of your Service name is your Service ID. Get the value in a text editor to put in a document.
Webauthn User Verification is a new, secure method for authenticating users on the web. It uses public key cryptography to create an encrypted connection between the user and the website that they are trying to access. WebAuthn is designed to be more secure than traditional username and password authentication,
How To Sign a Document Electronically

Use an electronic signature service: There are many online services that allow you to securely sign documents electronically. These services often use encryption technology to ensure the document is secure and can be verified by a third party. Use a digital signature: Digital signatures are an advanced form.
Build the backend
You have requested two backend-endpoints:/send-notification and /verify. This endpoint will be added to your site shortly.
Verify the OTP submitted by the user
It also received/verified OTP's e-mail address as well as the user's email address. The endpoint will verify whether the submitted email is correct by requesting the Twilio verification API. The result will also show the status and the verification check. The verification process has three statuses: approved or cancelled. Create an update to verification otp.js folder. The following code will be used to check the phone number and the OTP provided by the user. The application creates a Response Object which returns a check for validation. This is the response and its response.
High read rates: Unlike email, app notifications or other forms of 2FA, SMS are read more, especially while awaiting an OTP. How does SMS OTP verification work? User requests to verify by clicking on the ‘verify' button on your website or app. A unique OTP is generated in your backend system.
The technology has been around for over 25 years, and most mobile phone users are comfortable using it. For enterprises, too, it offers several benefits. Security: Unlike passwords, SMS OTPs are temporary, protecting customers from abuse later. As they are sent to a user's registered mobile number, it is unlikely to have been intercepted on the way.
Send the verification code to the user
The end-point received the'send-notification' and the Twilio verification API identifies the phone number of a user that he/she is sending to. Upon completion of verifications, this step takes place. Within the verify-demo/function directory you can create a file known as sendnotification.j. Copy this code and paste it in your new send-notification.js file: Twilio Functions provides the possibility for accessing request requests for a particular event object.
Using a mathematical algorithm where the new password is based on a challenge (e.g., a random number chosen by the authentication server or transaction details) and/or a counter. Time-synchronized Edit A time-synchronized OTP is usually related to a piece of hardware called a security token (e.g., each user is given a personal token that generates a one-time password).
What is my OTP code number?
During the operation of the OTP transactions the corresponding six-digit numerical code is transmitted via SMS. OTP is necessary to authorize transactions – registering beneficiary bank accounts with other banks. Payment of bills.
This token may be a proprietary device, or a mobile phone or similar mobile device which runs software that is proprietary, freeware , or open-source . An example of a time-synchronized OTP standard is Time-based One-Time Password (TOTP). Some applications can be used to keep time-synchronized OTP, like Google Authenticator or a password manager.
he one-time password can be delivered to a user through several channels, including an SMS-based text message, an email or a dedicated application on the endpoint. Security professionals have long been concerned that SMS message spoofing and man-in-the-middle (MITM) attacks can be used to break 2FA systems that rely on one-time passwords.